« Huge Spam Spike on 9 August 2007 | Main | New Pump-a-Dump Spammer Technique »
| Home | The Book | Training | Events | Tools | Stats |
August 11, 2007
Thank Goodness English is a Difficult LanguageHere is the opening of a message that would grab the attention of any PayPal account holder:
Reply-To: <no-reply@paypal.com>
From: "PayPal Corp."<service@paypal.com>
Subject: User Agreement Violation (ID PP133320)
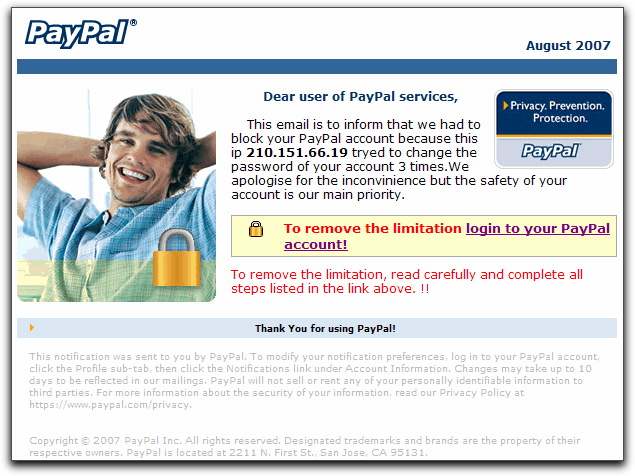
The entire message, however, is contained in an image. Text in the image attempts to convey the importance of logging into one's PayPal account right away. Unfortunately, the text is, um, not so good in the grammar and spelling departments:
Although the image appears to have distinct clickable links, the entire image is a single link. The destination of that link is a page inserted into hijacked web server (otherwise unused at the moment). That page then redirects any visitor to the phishing page asking for the PayPal user ID and password. Unlike most phishers recently, this guy bought a domain name (99% chance it was with a stolen credit card) and used a free hosting service to put up his phony site. The domain name is one of those lookalikes, where he uses "paypai" to look like "paypal." That is sooo 2004.
For the record, my PayPal account was blocked about a year and a half ago because someone tried (without a "y") to access my account, trolling unsuccessfully for the right password—details here. PayPal does not send out a notice when this happens. You discover it when you try to log into your account the regular way, and you are denied access. PayPal does record the IP address for each account access, but knowing that a South Korean computer tried to hack my account wasn't much help in tracking down the perp. Using a non-public and unique-for-my-PayPal-account email address has solved that problem.
I'm glad to report that in the time I've been writing this dispatch, the hosting service for the actual phishing login page has taken the site down. Woohoo! I'm sure the phisher will soon use another stolen credit card to create yet another domain (if a few aren't already standing by in inventory), and the redirector page will be changed accordingly.
I doubt, however, that he'll buy any English language lessons.
UPDATE (12Aug2007 AM) — Exactly as I had predicted, the same phisher has set up a new site, using a one-character-different domain, still containing "paypai" in the domain name. I haven't received a phishing message yet, so I hope the hosting company (same one used for the first site) is awake this Sunday morning to shut it down before the email drops.
UPDATE (12Aug2007 PM) — With the second site shut down, we're now onto the third "paypai" domain name and site. I wonder how long this game will go on.
UPDATE (13Aug2007 AM) — The third domain/site was shut down last night, and no new one has appeared in its place in the last 12 hours. Oh, poor little phisher.
Posted on August 11, 2007 at 05:33 PM