| Home | The Book | Training | Events | Tools | Stats |
February 27, 2005
Self-defeating Spamming
I might have more faith in so-called search engine optimizers (SEOs) if there weren't so many of them spamming the heck out of the Internet. Their service is supposed to help your Web site show up earlier in the pages when a Google, Yahoo, or other user searches for keywords associated with your site's content.
I spotted a spam message from an SEO outfit that calls into question how effective this company might be. The message begins:
We were just searching for "car, car insurance, car rental, used car, new car, auto trader, and auto" we came across your website and we thought that your company would be interested in further improving your search engine visibility, web traffic and on-line sales.
Now, this message was directed to my other domain, dannyg.com, which is dedicated to supporting my programming-oriented books. I don't sell cars or car insurance; there isn't even a blog-type piece in which I describe buying or renting a new or used car, much less any participation in auto trading.
My site includes a Google-based search service. Applying the prescribed search query to my site yields zero results.
I searched my site for "car" and found two hits. One is in an ancient opinion piece in which I compare a car and a hog (porcine type). The other is in one my JavaScript examples called "Decision Maker," where I comment that one could use it to help decide about which car to buy. The default example, however, is choosing a FAX machine. For "auto," there were a few more hits, but only one (again, from an ancient opinion piece) has anything to do with transporation.
What's disturbing about this oh-so-typical spam bait is that the message tries to sound personal. "We searched" blah blah "we came across your web site" blah blah. Makes it sound like there might have been some type of human intervention here. There can't have been. There's no way on Earth that the said search string found my site; nor would any rational being think I'd want to associate my site with those keywords.
It's all Scrape (the address) and Spam.
Besides, I don't want my site to be any higher in the search results for cars and autos, thank you very much.
Posted on February 27, 2005 at 11:17 AMFebruary 26, 2005
More Thesaurus Roulette
Following a similar format to the spam described here, one of today's suspects fills in the blanks with synonyms to a point where I can't really tell what they're selling (and I won't follow the link to find out). In the text-only view is this gem:
Finest market for your grants.
Distinguished products at a most sensible cost.
I know, it sounds like one of those "we'll tell you where all the grant money is" scpams (yes, I'm coining a word), but I think it's the same medz spammer (different spamvertised domain, but what else is new?) as before. The subject of this pearl is ambiguous: "We can furnish the delectation of having the top-quality." Yet the "quality" buzzword is usually associated with medz or leadz spammers.
Here, then is the HTML version:
Best source for your bestowals.
Prominent things at a most judicious cost.
Egadz!
Posted on February 26, 2005 at 12:11 PMFebruary 23, 2005
YASMS*
I hate it when a spam message slips into my inbox, but at least this one was easy to spot:
I've been aggressively forwarding copies of especially mortgage spam to the U.S. Federal Trade Commission "refrigerator" (spam@uce.gov) to add more heat to their evidence embers. None of it is CAN-SPAM compliant. And despite prosecutors' recent success at shutting down reportedly one of the worst in this category, that action seems only to have encouraged more mortgage spamming.
Not responding in any way to these guys would encourage them to find another line of work.
---------------------
*Yet Another Stoopid Mortgage Spammer

I don't know where to begin with this one. It's a medz spammer who, in my estimation, is not an English speaker and has thus fallen prey to the weirdness of the Babel Fish translator, or Roget's Thesaurus run amok. But there's more to the story.
First comes the incomprehensible Subject: line:
Subject: Such specific -- elfin price!
Oh, okay, I get it. "Elfin" must be a synonym for "small" or "tiny." But the first part escapes me.
I'll get to the content in a moment, but the underlying premise is that the medz will be coming from India. The domain name for this ad is hosted in China, and the domain is registered (supposedly) to somone in Australia. Something tells me, however, that the registrant's regular email address account name (at a free Web mail service) isn't "lkjlljsdfalkjlasdfasdf," like it says in the registration.
Now we get to the message. If you were to read the suspicious message in your email client's normal view mode (not a good idea, as Spam Wars readers know), you wouldn't see that there are two versions of the message: one for text-only viewers and another for HTML viewers.
The text-only version says:
Seek medicine flat from Food and Drug Administration authorized factory-owner in India. Reserve up to 55% on our narcotics.
(Oh yah! I'm sure it's easy for a consumer to check with the FDA that an Indian factory, whose products are being sold through a gibberish-dot-com, is "authorized." And the FDA must work really, really fast because the domain name was issued [drum roll] yesterday.)
Here's the HTML version:
Ask for pharmaceuticals directly fromFood and Drug Administration accepted manufacturer in Republic of India.
Reserve up to 70% on indian medication.
Comparing the language of the two, you can see the synonym roulette in operation (seek/ask; flat/directly). The use of "narcotics" in the text version seem a bit jarring to my eye (and I'm no narc).
But how 'bout them discounts! You can save so much more on the HTML version of your medz. Uh huh. The links from the two message segments are absolutely identical.
Stupid spammers won't ever learn to make their offerz credible. Keep up the lousy work, because it makes it so much easier for us to completely ignore you. ZERO RESPONSE for you!
Posted on February 23, 2005 at 09:39 AMFebruary 21, 2005
"Spam Wars" Notes
Two items of interest today.
First, for those potential readers who have been holding out for a sample chapter, I've posted an Adobe Acrobat (PDF) file of several selections from the book (and the complete index). I don't know if it's because I had to create a second-generation Acrobat file, but the quality of the sample page text isn't like the crisp real thing. My apologies for that.
Second, Spam Wars readers know about my notion of the sanctity of one's email address and, sadly, how spammers violate that sanctity with great glee and frequency. On page 230 I talk about how Australia's antispam law limits what kind of consent can be inferred by someone obtaining an email address on a Web page.
Canada has just chimed in on the same subject. Read about Canada's Privacy Commissioner ruling, which implies similar limitations on how a publicly posted email address may be used by unsolicited emailers.
This is all well and good, but from my reading of what happened here, the case and ruling do nothing to thwart the worst of the worst harvesters (and the millionsCDs they've created over the years). In this case, a readily identifiable, brand-name, legitimate business got caught with its hand in the spam tin. Meanwhile, mega-harvesters and big "disguised" spammers are ROTFL (Rolling on The Floor Laughing), taunting with "Catch us if you can."
Posted on February 21, 2005 at 03:52 PMFebruary 16, 2005
Phishing By Phone (Phphishing?)
I just heard of a scam that has probably been going on for some time but just reached my radar screen. This time, the scam doesn't involve email, but it has all the hallmarks of the phishing scams we've come to know so well.
In this case, a retiree gets a telephone call from someone claiming to be from a bank asking to verify some information. Even if the retiree advises the caller that he or she has no account at that bank, the caller adamantly says that there is a $75 credit on the books, and they need the personal information to confirm that the funds belong to the retiree. The "bank" doesn't have the information, but requires all the information come from the retiree.
Sound familiar?
One recipient of such a call I know was fortunately suspicious, and refused to supply any of the information. The scammer, who had started the conversation with a friendly tone, then threatened to report her to the state's Attorney General's office. This tactic is just like the one used by numerous investment scammers working from telephone boiler rooms. To me, it's a form of elder abuse. Unfortunately, a lot of lonely, polite, and easily confused seniors get taken in by these scams every day.
I know the 419 (advance fee) scams originally started many years ago through postal mail and switched to email with the times (although I also got a junk fax with a 419 scam letter last month). Perhaps someone in law enforcement can tell me if phishing started by phone and migrated to email, or vice versa. I suspect that today's email phishing gangs have opened up a more facile marketplace for the stolen personal identity info.
And I don't expect phone phishers to honor the FTC's Do-Not-Call Registry. The scammers will be on different numbers before anyone could investigate.
Posted on February 16, 2005 at 03:47 PM
When you're a spam and scam fighter, your pet peeve list is mighty long. But one that ranks up pretty high on my list is the fact that the domain name registration system seems to invite fraud on a huge scale. Does any domain registrar (outside of those responsible for .gov, .edu, and .mil) do any vetting of their applicants?
It sure doesn't seem so.
On the one hand you have domains being registered with names like "paypal" embedded within some other words and hyphens, and the registrant is not PayPal or eBay (which owns PayPal). The chances that this domain will be used for some phishing scheme is pretty high. Yet because no human looks at registration info before a domain is granted, the form can list Dogbert as the owner, and no one will know until the site is up, running, and ripping off visitors.
Speaking of phishing domains, an eBay one just came in. The real link is to a gibberish domain whose registration I checked via the widely available "whois" lookup. Here are the identity fields supplied by the registrant (email userID disguised by me in case it's a valid address; street number also disguised by me):
owner: wfwef dfsdfsd
email: <x>#hotmail.com
address: <x> East 22nd Avenue
city: 36542
state: --
postal-code: 36542
country: US
The registrar is a Danish domain reseller for Joker.com. The phishing site is also hosted in Denmark, which leads me to think the phisher knows Danish and may be from there—and not from Gulf Shores, Alabama, where the ZIP code is located. But I don't think anyone from Denmark is named "wfwef dfsdfsd," or as I call him, "Lefty" (check your computer keyboard).
This is nothing compared to even more egregiously bogus registrations I've seen, which use all 9s for phone numbers and postal codes for example.
The automated registration process is so easily scammed, that it makes those of us who fill out the forms honestly look like chumps. Of course the scammers don't expect the domains they register to last long—just long enough to pull off their scam and move on to the next one (this phisher's domain was registered only three days before I got the phishing message). Those of us who do the right thing want to renew our domains and perhaps build some domain-brand identity over time. We want to be contacted at renewal time.
And if you think it's easy to get phony domain registrations cancelled, think again. You can file a complaint, I mean a "Whois Data Problem Report" with the Internet Corporation for Assigned Names and Numbers (ICANN). Just don't expect resolution of the problem anytime soon. The report winds up in the hands of the registrar, who may or may not act on it. Sure, ICANN has all kinds of advisories that sound like registrars have to act relatively promptly. In truth, you'll find more teeth in a hen's beak.
Posted on February 16, 2005 at 01:37 PMFebruary 14, 2005
Phish Are Jumpin'...
I've referred in other posts here that I sense the availability of "ready-to-run" kits for wannabe phishers. Too many batches of messages have too many similarities to be the creative work of a diverse bunch. This means that the crooks at the root of the scams hire underlings to do their mailings and gather the phished data (and thus distance themselves further from any possible law enforcement).
I'm starting to wonder, however, if there are so many little phishers out there that the system is starting to bend under its own weight. In checking my overnight email server log, I found no fewer than nine phishing messages aimed at my address:
- 6 Washington Mutual (wamu)
- 2 PayPal
- 1 Citizens Bank
These are just the ones that weren't summarily rejected at my server because they were addressed to invalid and corrupted user names that circulate widely on "millions CDs" among spammers.
If I were a wamu customer, I would have received so many phishing messages in the last year that it's highly unlikely that one of today's messages would convince me to "click here" to yield my private info. The odds of one of these messages finding a new wamu customer who hasn't seen these messages before must be minuscule. Just as real fisherman can overfish a region and ruin future catches, too many phishers must be overphishing various institutions, causing (I hope) much lower yields.
The reward for tricking a phishing victim, however, can be large. A case in point is a Bank of America victim who had $90,000 lifted from his account (and is suing BofA—but that's another story). At that rate, it doesn't take too many catches to make it a good day at the ol' phishing hole. And that's why they'll keep phishing in the hopes of reeling in the catch with the diamond in its stomach.
Posted on February 14, 2005 at 09:11 AM
A mortgage spam came in today that is so "out there" that I had to share it with you. It asks me to visit "our secure site" to fill out an application (the link is to a regular http: site, not a secure https: site). The form, I'm told, "does not ask for any sensative [sic] info." Yet, after filling it out, I'll get a 180,000.00 (no monetary units) loan from "one of our lenders."
If I assume they're talking dollars here, they must not know that I live in an urban California area. That amount of money would cover, perhaps, a one-car garage of the homes I see for sale. What I'd like to know is what kind of lender would grant a 180K loan (in any denomination, including yen) without having extracted some kind of "sensative" info from me? Neither lenders nor loan sharks work without knowing plenty about their borrowers.
In case the deal so far has not convinced me, the message contains a "pps" (I guess the P.S. got lost somewhere). Read it aloud:
pps: It does NOT cost anything, just fillup a online form - we request you to take just 2 minutes off your valuable time.
Based on the details of the clickable link in the message, this was sent (through a DSL-connected zombie at Ameritech) as an affiliate mortgage lead spam. It's someone waaay down the ladder in the spam chain, probably someone who responded to a "make money on the Internet in your underwear" spam. He or she gets paid for every form that you "fillup," whether the info is valid or not (and perhaps for every visit to the site). It only encourages the spammer to continue. Wouldn't it be great to reward this stupid spammer with Zero Response? Anything to get him or her to put on some pants.
Posted on February 14, 2005 at 09:01 AMFebruary 13, 2005
Free Vacation Slime
As much as I jump up and down to proclaim that the spam problem is about consent, and not content, it's the content that gets unsuspecting recipients into trouble. When I see the content of a spam message ooze with lies and deception, it makes my blood boil. I know that there will be people out there who will not only believe the garbage, but will respond. Yikes!
Today's thorn in my side is a message whose subject reads: "RE: Your Trip". The From: field lists only an email address, someone named "Anoush" at a domain I've never heard of (freshly minted in late January of 2005).
The message body tells me that I had signed up for a free Florida trip last year (trust me, I didn't), but the trip had to be cancelled due to the hurricanes. Wonder of wonders, they are going to give me a new free trip—10 days with tickets to various brand name attractions.
The message is signed by "Pete" (what happened to Anoush?). Clicking a link will let me redeem my tickets.
The link is to yet another domain name. This one was minted just a few days ago. I guess the hurricanes blew away their old domains (where I supposedly signed up last year).
Anyone who falls for this bait finds him/herself facing a Web page form asking for complete name, address, email address, income range, and other personal info, including credit card type (but not the number on this form). Oh, yeah, and the fine print suddenly advises that filling out this form (in its entirety, or else) lets one "qualify" for the trip. And you agree to receive additional contact by email or phone.
So what gives here? I'm not about to give up my golden info to find out for sure, but this looks a lot like an all-too-common data gathering scheme. By filling out this form, you not only supply these guys with fresh demographic data, but you'll assist services that try to link up geographic addresses with email addresses (called "email appending"). This turns your email address into veritable gold (not for you, mind you) because it lets your email address be sold (and sold and sold and...) as a demographically targeted piece of data.
In return, here's what you get: 1) More spam to your email address because you registered with an outfit that will have hundreds of "partners"; 2) Telemarketing calls because you gave them permission.
The free trip? If you get there, send me a postcard. I won't be sitting by my mailbox in anticipation.
Other than open source software (like the Firefox Web browser), there isn't much in the way of a Free Lunch on the Internet. I mean even my little Web site here—assuming you find something here of value—relentlessly hammers you with a "Buy Today" ad in the upper left corner. Any spam message that promises something for free will make you pay one way or another. If you have to give up even the slightest bit of personal information in the process, you should consider the price way too high.
Posted on February 13, 2005 at 05:39 PMFebruary 09, 2005
Stupid Lottery Spammer
According to today's spam, I've won yet another international lottery. C'mon, guys, my mattress is already overstuffed from the millions of euros won in earlier lotteries. Give someone else a chance!
I've written about this stuff before here and here, so there's no need to go into details. But this time the sender took some of the oomph out of his scam by including—in plain view in the To: field—the list of 100 addressees of this mailing. Does that mean that each of us had the same "winning number," or do we split the half-million euros among us? The barely English message gives little clue.
The creepy part, though, is that I recognize several addresses in the list. Lots of good computer industry folks in this list: Dan Farber, David Coursey, Dave Winer, Dan Shafer, Michael Miller, Doug Baron, and Steve Riggins, to name several. And then there are some really old addresses for Chris Gulker and Bud Colligan that must have been invalid for at least five years. I can only assume that these addresses were harvested by a worm in an infected PC somewhere, and probably the machine of someone who knows these folks and me. It was spooky enough for me to check my own address book to see if the addresses are in there. Most are not (plus I run an antivirus-protected Mac, making the likelihood of infection extremely remote).
While the list of addressees might be valuable to someone trying to get the word out about something in the computer industry, I get the feeling they're mostly experienced computer users who wouldn't give this lottery scam a half-second of thought. What a complete waste of bits.
Posted on February 09, 2005 at 07:58 AMFebruary 08, 2005
Step Away From the Mouse Button...
Since a lot of spammers already break the laws of one country or another, it's not surprising to see them breaking the laws of HTML to launch a trick on unsuspecting users. Okay, HTML doesn't have "laws" per se, but the published international standards (officially, they're called "recommendations") are intended to encourage a level of consistency and reliability across the Web.
Well, we can dream.
Back to spammers, they've been using HTML in their messages ever since the audience had achieved a critical mass to make it worth the bother. As spam filtering improved, the filters got better at recognizing spammers' HTML tricks, such as embedding white (or near-white) text on a white background. Some spammers "progressed" to including only an image (whose contents bore all the spamvertising text) surrounded by a clickable link. But then the filters got suspicious of that combination. And on and on.
I've recently seen a couple of messages that ignore an HTML requirement for embedded images, and the effect is a potential hazard to recipients. The trick is to define an image element that has no image source address defined for it. With the help of just a little additional source code, this source-less image creates a transparent layer atop the entire message body. The "image" is made clickable, with the destination being the spamvertised Web site or, as indicated in some recent posts, someplace extremely dangerous.
The bottom line with this trick is that if you even accidentally click anywhere in the message body, you'll be off to...we're not talking Neverland here. The spammer is taking advantage of HTML rendering engines in email clients that try to do their best even with invalid HTML coding.
Unlike Webmasters who try to build legitimate traffic to their Web sites by creating valid pages, something tells me that the spammers don't care that the HTML Standards Police are out to get them.
Posted on February 08, 2005 at 02:46 PM
A recent medz spammer is pulling out the stops to prevent content-based spam filters from spotting his garbage. In Spam Wars, I describe Message Trick #18 (pp.160-161), which entails using what are called numeric character references to disguise URLs (and which may be decoded using the deobfuscator tool I provide at this site).
Related to those numeric references is a way of adding various symbols to HTML body text—like the one that let me use an em-dash in this sentence. Or the copyright (©) symbol. Pretty handy stuff.
Among the characters that can be represented this way are a bunch of Greek characters, which might normally show up in things like math formulas (and a πr² to you, too). A lot of Greek characters look like Latin characters, even if they don't sound the same. An uppercase rho character looks like a capital "P," and an uppercase alpha looks just like a capital "A."
(It's just a coincidence that I talk about this one day after discussing another technique that is based on the same concept, called a homograph. This one, however, is simply an elaboration on the old trick that substitutes zeros for uppercase Os.)
This Greek substitution trick is how today's medz spammer spelled "PHARMACY" using the following character entities:
ΡΗΑRΜΑCΥ
When given certain font family and styling parameter, this gobbledygook presents the following (I'll let your browser do the rendering):
ΡΗΑRΜΑCΥ
The uppercase upsilon at the end makes kind of a weak "Y," but you get the picture.
More importantly for the spammer, until users' filters learn about this trick, some messages will probably sneak through.
Rats!
Posted on February 08, 2005 at 02:11 PMFebruary 07, 2005
Reciprocal Link Spam
So some guy with an online shop for electric scooters spams me to set up reciprocal links on our Web sites (I point to him; he points to me).
The information and services offered on your site would be of great value to our visitors, and I believe, your visitors would find great value in our sites. Because yours and our web sites are complementary rather than competitive, we see the synergy here as an opportunity for our mutual benefit.
This piece of spam was addressed to my dannyg.com domain, but I think it's fairly obvious from my site's home page that I'm no fan of spam. The prominent link to this site should put an exclamation point on that. I can guarantee you that this sender didn't visit my site before sending the spam message.
(The message's headers and other clues within the message indicate that the message originated in India, and the whole spam effort is being launched by a "search engine optimization" firm based in the U.S. It's possible that Scooter-Boy fell prey to other spam from the optimization outfit that promised to boost the company's search engine ratings.)
The only thing that his products and services have in common with my products and services is that his scooters run on electricity, and so do the computers my visitors use. Maybe I should give him a special URL to post to his list that points to a page that advises visitors not to buy from the scooter guy because he's a spammer. I'm not about to provide Scooter's URL here to boost his rankings ("You probably think this post is about you, don't you?").
While I'd dearly like to get my sites high up in the Google rankings (which is aided by other sites linking to my sites), I won't buy, con, or spam my way up the ladder. If others find me and like what I write, then I hope they'll provide pointers this way. I'm sure there are plenty of folks out there who think I'm crazy and/or stupid for not playing the search engines for loopholes. So be it.
Posted on February 07, 2005 at 04:15 PM
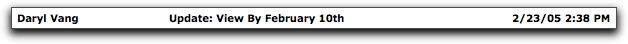
I didn't like the trend of this two-message sequence:
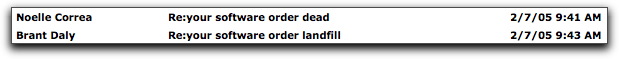
Blocking further messages in case it gets worse. Posted on February 07, 2005 at 11:05 AM

No sooner do I finish a Dispatch posting about the dangers of clicking links in spam than I read the details of an exploit that invalidates a lot of the advice about phishing sites. For once, however, the exploit affects browsers other than Microsoft Internet Explorer.
Here is the background:
Acknowledging that the world does not all speak English or use Western characters in their languages, Internet standards bodies developed a way that allows other character sets to be used in domain names. The idea is to make a domain for someone in, say, Greece, more comfortable with a Greek domain name, rather than using a foreign (i.e., English) character set.
It turns out that some characters in some non-English alphabets look like English characters when the computers or software equipped with those character sets display them on the screen. I'm speaking beyond the old trick of substituting zeros for uppercase Os. Modern browsers equipped with this International Domain Name (IDN) capability display the rendered version of the URL in the Address box, as well as in a Web page body and status box during a mouse rollover of a link.
For a scary (but harmless) demonstration of this technique, use a browser such as Firefox, Netscape 7.x, Safari, or Opera to visit a special page set up at the Schmoo Group. There you'll be able to click on links purporting to take you to Paypal—including one that links to a secure page. If you are running browsers other than IE, the Address box will show what appears to be "paypal.com" (including a real secure lock icon in the https version) but in actuality is "xn--pypal-4ve.com", the English equivalent of the specially coded URL.
What does this all mean?
Although I haven't yet seen examples of this exploit used in phishing scams, it may turn up. It's frightening to think that unsuspecting phishing victims will not be aware that the entire process—bogus email leading to a bogus site bearing all the right hallmarks on the surface—is under control of scammers. The factor working against wide use of this exploit is that most of the world uses IE, which doesn't support the new IDN standard in either Windows or Mac versions.
(Lots of Web developers slam Internet Explorer because it doesn't support enough standards, but this time it escapes an exploit for that very reason. Oh, the irony!)
If you take the advice I give you in Spam Wars and inspect suspicious messages correctly, you would spot that something is wrong with the URL before you ever clicked it. In the case of the PayPal spoof above, the source code shows the link destination as being "http://www.pаypal.com/", a sure sign that something stinks.
This problem appears to be not so much a browser bug, as a flaw in a standard (known as early as 2001). As some users flee IE/Windows to escape vulnerability after vulnerability, they find themselves merely jumping from one frying pan into another. Shields up!
Posted on February 07, 2005 at 10:43 AM
The Web is, indeed, World Wide, which leads to visits to sites that are not written in your native language. If that happens to you a lot, you have probably already encountered translation services, such as Babel Fish. One of my hobbies has a huge following in Europe, with numerous Web sites in a language with which I have only a passing acquaintance. Thus, I use Babel Fish quite a lot.
I also know that Babel Fish doesn't always perform, um, glowing translations. It's not uncommon for the translation to be tortured, if not incomprehensible. Having seen its results, I still find it useful to get some other language into English to give me a clue about what's being said, but I would never trust it to convert my prose into something I'd send to a person.
One of today's spammers wasn't so cautious.
Here is the Subject: line for this mystery spam:
Subject: You need to render the delight of holding the best
Mmmkay. A safe check of the message's source code shows two different messages, one for non-HTML email clients, and one for HTML-capable clients. The non-HTML version (sans spamvertised URL) reads:
Top-quality source for your gifts.
Famous value at a most reasonable worth.
The HTML version reads:
Best website for your presents.
Great products at a very judicious cost.
Audit costs
This is precisely the kind of gibberish you'd see by translating some probably good non-English prose into English via Babel Fish. From what language? It's hard to say.
Each message had a separate URL and domain name. Both domain names—about 10 random consonants spelling out no word of a human language—were freshly minted just yesterday. Registration info for both lead to addresses in Japan and Oklahoma, although the Oklahoma registration is completely bogus. The Japanese one has all the right stuff in all the right places, but it, too, could be bogus. The message was sent through a proxy or Trojaned PC in South Korea.
As for what one actually gets by clicking the link, it's hard to say. I won't do it from any of my own computers, but through some snooping, I'm rather unnerved by indications that the servers appear to be checking whether the browser accessing the site is running Windows XP SP2. This could mean that the site is looking for pre-SP2 versions to infect with Bad Stuff or trying out an infection targeted at SP2.
Like the Sony camera business of last week (which may have reared its ugly head again under a different account at netfirms.com), this spam—gibberish or otherwise—points to how dangerous it is to click any link in any unsolicited message. Infections don't have to arrive as attachments anymore. Clicking a spam link is like lighting a fuse to a bomb whose concussion will take out your computer. In any language:kaboom!
Posted on February 07, 2005 at 09:23 AMFebruary 03, 2005
More Hijackings Followup
As a followup to a posting a few days ago, it has been suggested that the Bad Stuff installed by visiting the Web site I described is a Trojan horse type of program of the "Banker" family. This Windows malware typically sits in the background and monitors your browser activity. When you visit a variety of financial institution Web sites (the program contains a list of targeted URLs), the background program monitors your keystrokes (sometimes taking screenshots), and thus captures your log in user ID and password.
I think if everyday email users knew how much personal damage a simple click on a link within a spam message could do, they'd stop clicking email links—even from sources they trust. That it took 43 hours for the site's ISP to take down the account is a crime in itself. The site may be down, but the Trojan certainly continues to live in its infected machines, sending its captured treasure to who-knows-where.
Posted on February 03, 2005 at 09:00 AM