| Home | The Book | Training | Events | Tools | Stats |
August 29, 2007
Postal Spam
In my postal mailbox today is the closest thing to email spam that I've ever seen delivered by the post office. It's an orange post card addressed to me "or current residents"—the postal equivalent of an indiscriminate non-personal message.
As I discuss at length in Spam Wars there are many differences between junk postal mail and spam, even when both are promoting a legitimate product from a legitimate sender. The biggest difference is that a postal mail sender incurs real costs in printing the piece and getting it into the postal system. The orange card I received had a "Presorted First Class US Postage PAID" indicia where the stamp usually goes. The USPS requires hard cash up front for these kinds of mailings, so the sender did shell out some cash to make this mailing.
On the back of the post card (there were no other markings on the front) is the following message:
CONGRATULATIONS!
You have won a FREE GIFT!
Call IMMEDIATELY to receive your gift.
1-800-728-xxxx
(1-800-SAVE-xxx)
Absolutely FREE
J.E.I.
That's it. No idea what the gift is, who "J.E.I." is, or what the catch will be to collect the free gift. Who knows, it could even be one of those scams that redirect seemingly toll-free phone numbers to offshore premium phone services that dump the charges onto the caller's phone bill (illegal in the U.S. now, but that hasn't stopped crooks).
I Googled the phone number and came up with several hits. Some older pages point to a home improvement business in Hayward, CA. Another site lists the number among a ton of numbers associated with telemarketers.
The text on the back of the card is just so spammy that it would be more at home in my email server's trash bin than my mail box. If the sender won't identify himself and be honest about the pitch, screw him. I am, however, stoked that it cost him 30-50 cents (printing, list rental, postage) to get that orange post card into my recycling bin.
Posted on August 29, 2007 at 01:52 PM
I have updated the Training page. The page includes a link to a new downloadable PDF brochure about the Email Safety 101 course.
Posted on August 29, 2007 at 11:49 AMAugust 26, 2007
Stormy Weather
The so-called Storm worm continues to mutate, using more and more believable social engineering tricks to lure unsuspecting users to perform risky behavior—notably to install a Trojan on their PCs that can do anything from installing keyloggers to surrendering the machine to a botnet controller.
Last week saw a ton of simple email messages that provided a login and temporary password to join a host of different types of organizations. Everything, of course, was a complete lie. Visiting the linked (and hijacked) site caused a Trojan to download.
This week, the conveyance of choice is a message that is similar to the types you get everyday from friends and relatives, telling you about some cool YouTube video:
Subject: LOL, that is too cool.....You need to take this offline, it is in everyones email. :-( check it out yourself http://www.youtube.com/watch?v=BbEor9cWCQ4
Underneath the bogus YouTube URL is a real link address to a server that displays a real YouTube logo (sourced from youtube.com). The destination site silently tries to download the Trojan. If the automatic download fails, the web page will lure you further:
Your Download Should Begin Shortly. If your download does not start in approximately 15 seconds, you can click here to launch the download and then press Run.
The "click here" link downloads a file named video.exe, an executable file that will likely cause you untold grief if you run it on an unprotected Windows PC. Unfortunately, in these days of zero-day attacks and continuously morphing Trojan packages, there is no guarantee that any PC (or Mac or Linux box for that matter) is protected.
The best protection continues to be a refusal to click links arriving in unsolicited messages (email, IM, and even within closed messaging systems), especially from people you don't know.
UPDATE: There are probably dozens of message subjects and bodies, but here is another I've personally seen:
Subject: man, who filmed this thing?Posted on August 26, 2007 at 09:11 AMLMAO, I cant believe you put this video online. Everyone can see your face there. LOL take a look, lol...[bogus YouTube URL here]
August 22, 2007
419er's Revenge on 419-Baiting?
The Internet has plenty of sites run by folks who enjoy baiting advance-fee (aka 419) scammers. I won't point to any specific ones here, but they're easy enough to find through Google. They're funny for awhile (and enlightening to see how long it takes for the scammer to get money flowing his way), but I suppose I've seen enough of them to get just as tired of the jokes as reading the repetitive B.S. from the scammers over the years.
419-baiters engage the scammers via email (and sometimes by phone) to get the scammers' hopes up that they're reeling in a new sucker. The baiters typically make numerous outrageous claims about themselves, their families, and businesses, wondering if the scammer will ever catch on that "pancake farming" is not a real enterprise. Oddly enough, the scammer is so greedy that he or she doesn't even seem to react to the ridiculous claims, but keeps the scam going. In fact, many baiters have even gotten the scammers to take photos of themselves holding comically insane banners.
Going through my stack of spam messages trapped and held on my server today, I came across a Hong Kong (supposedly) advance-fee scammer who is either a) unfamiliar with English vernacular (a very high probability) or b) playing a prank on the potential suckers who respond. Here is the first paragraph of the oh-so-typical 419 come-on...typical except for the name of the now-deceased fictional businessman:
Greetings to you and your family.I hope you are having a blissful week.I am Mr.Joseph Chau of Investment Banking,Union Bank Of China.On July 6, 2004,our client Mr. Irvin Poot,a businessman,made a numbered fixed deposit for 6 (six)calendar months,with a value of Twenty million,Five Hundred Thousand United State Dollars only in my branch. Upon maturity several notice was sent to him and no response came from him. Another notification was sent early February and still no response came from him.
I recognized the last name. And here is Google's top-rated entry in the Urban Dictionary for that family name.
I like a scam that tells you up front that the whole thing stinks.
Posted on August 22, 2007 at 04:42 PM
I was reading an analysis of the injunction that a federal district court, based on claims in a law suit brought by MySpace. While I had seen accounts of this about a week ago (an interesting legal analysis can also be found here), there was a quantitative point that was news to me. And rather disturbing.
According to today's posting, the defendant had allegedly created a phishing-type system that led initial recipients of MySpace messages sent from his 11,000 MySpace accounts to log into a MySpace lookalike site, where—get this—320,000 users gave up their usernames and passwords.
320,000!
O. M. G.
I don't have a MySpace account—more than anyone could want to know about me is splattered across my web sites—but it is apparently pretty popular among the younger set. I'd love to see an age distribution chart of the 320,000 users who were so eager to hand over their accounts to a stranger. My assumption (yes, I know to "assume" makes an "ass" out of "u" and "me") is that those who did this skew to a lower age than the entire MySpace population.
It points to one of the greatest challenges facing privacy protection and Internet security. Younger folks are less likely to be suspicious of potentially harmful activity orchestrated by strangers with Brandy. Thus, they are more likely to go clickety-clickety on unknown links and attachments arriving via unsolicited email from senders they don't know. Ooh, a free video game...Install! When faced with a logon screen that looks anything like ones they've seen before, they are eager to ace the test by entering data they have down cold.
We obviously can't rely on parents to teach their children well about Internet scams. Mom and Dad too busy ordering Viagra from China and planning how to spend their commission from extricating twelve million dollars from a lock box in a Nigerian bank vault.
Posted on August 22, 2007 at 09:38 AMAugust 17, 2007
Attack of the Clowns
On a typical day in the neighborhood, my dannyg.com email server suffers between 50 and 200 attempts to relay spam or malware. All of those attempts are blocked, of course, and in the grand scheme of things, that volume isn't such a big deal. But my eyes popped out of their sockets today when I saw that the volume increased to over 23,000 for yesterday.
I dug into the logs to see what was happening. In this case, there were 23,454 attempts to relay, all originating from the same IP address, spaced over a 2.5 hour period. That comes to an average of 2.6 attempts per second, not exactly a Denial-of-Service attack.
The IP address is owned by Deutsche Telekom, and more specifically, T-Systems Business Services (whose logo looks like that of T-Mobile). I've asked for an explanation, but I doubt I'll get it.
It's obvious that the attempts were made through an automated bot of some type—a really stupid bot that won't take "No!" for an answer. 23,453 times.
Posted on August 17, 2007 at 07:59 AMAugust 14, 2007
New Pump-a-Dump Spammer Technique
For the past couple of months, the antispam community has been abuzz with the spammer tactic of sending the body of the spam message as a PDF (Adobe Acrobat) file. Tons and tons of legitimate PDF files exchange hands via email every day, making it impossible to deploy a blocking technique that uses the attached PDF file as the signal to can the spam. From what I've heard, not every antispam software or service solution has been successful at building a profile that can distinguish a spam PDF from a ham PDF.
Just as that battle wages, I've seen yet another tactic over the last two days that makes spam detection even more difficult. The not-so-funny part is that the technique is very low tech.
The campaign is for the ol' penny stock pump-and-dump scam—a message that claims to convey inside information about a down-and-nearly-out stock whose price is set to "explode." The scammers have already bought the stock (often through hijacked/phished electronic trading accounts), and wait for the suckers to start bidding up the stock based on this bogus forecast. The scammers have their fingers hovering above the "Sell" button while greedy investors are hitting "Buy" buttons; when the stock starts to plateau (I'm talking over a matter of hours of one day), the scammers sell their holdings, leaving the rest with a stock that goes nowhere.
In looking at the day's chart for the subject stock, there was a flurry of activity beginning with a very large number of shares traded at the low price (the scammer's buy-in?), substantial activity as the price ramped up, and then a big batch of trades when the price had gone up about 10% (the scammer's sell-off?), at which point the stock dipped a bit. It seems odd to me that anyone smart enough to be an active stock trader would be foolish enough to waste his or her investment dollars filling the pockets of scammers. If the scam didn't work, the scammers wouldn't continue doing it.
Back to the spam technique.
It's obviously important for any spammer to get messages past spam filtering, be it on the server, personal computer, or both. The use of botnets to spew messages (illegally here in the U.S.) has made it more difficult to block messages solely on the sending IP address. That's why good spam filtering also utilizes content examination to score a message for its "spamminess." When a spam filtering service sees a lot of messages with the same content, it's easy to build a profile that blocks subsequent receipt of the same message. The trouble comes when the message changes its content slightly with every instance.
Spammers have known about this for some time, of course. The once-popular image attachment spam was modified so that each instance of the image had some extra pixels of "noise" in the background. Changing a few pixels would alter the "fingerprint" of the image, giving the spam detection algorithms headaches. The attached image, however, still caused spam detection software to take a closer look. Then came the move to the less suspicious PDF attachment, also varied with random noise.
Now, the pump-a-dump spammers have reverted to plain text, but still using a kind of randomization that makes it difficult for antispam software to obtain an identifiable fingerprint of the message. Here are excerpts from the 12 versions that got into my inbox overnight:
H+u*g,e N*e w's To Impa.ct C*Y'T*V
H_u*g e N_e'w*s To Impa'ct C_Y'T+V
H,u*g-e N.e-w-s To I mpact C'Y'T_V
H'u,g-e N*e*w,s To Impa_ct C+Y_T+V
H u_g-e N-e.w,s To Imp,act C Y.T'V
H-u g e N_e+w,s To Imp_act C,Y*T.V
H u+g,e N*e-w-s To Impac't C_Y,T,V
H*u_g+e N-e_w*s To Impac,t C'Y+T_V
H'u_g'e N*e_w_s To Impac.t C'Y*T,V
H*u_g_e N.e*w,s To Impac+t C.Y_T*V
H u,g'e N e'w-s To Impa_ct C*Y T.V
H-u'g_e N e*w s To Impa*ct C.Y+T.V
The entire message, including some public domain hash-busting text at the end, is written in this format. In this case, the random "noise" is in the form of spaces and standard symbols. But it doesn't take a Sherlock Holmes to understand the meaning of the message (way to go, human brain!).
Subject: lines for the 12 messages were all different, consisting of sentences lifted from a variety of sources (three in German, the rest in English). Each message was sent by a different botnetted computer. Even the obfuscated hashbusting text in each message was different.
The only "inside information" that pump-a-dump spammers have is that there are gullible investors out there. Duh.
Posted on August 14, 2007 at 09:04 AMAugust 11, 2007
Thank Goodness English is a Difficult Language
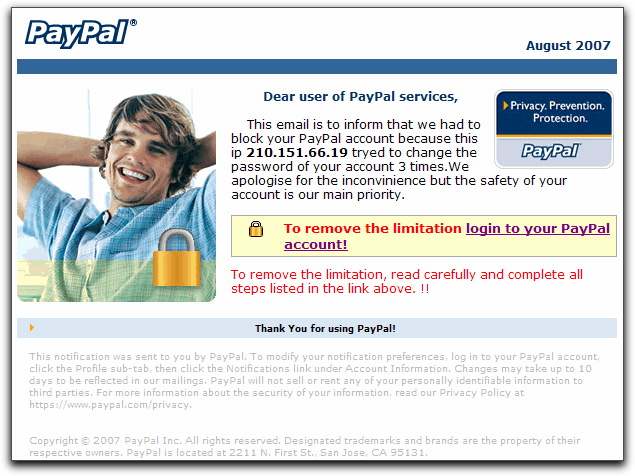
Here is the opening of a message that would grab the attention of any PayPal account holder:
Reply-To: <no-reply@paypal.com>
From: "PayPal Corp."<service@paypal.com>
Subject: User Agreement Violation (ID PP133320)
The entire message, however, is contained in an image. Text in the image attempts to convey the importance of logging into one's PayPal account right away. Unfortunately, the text is, um, not so good in the grammar and spelling departments:
Although the image appears to have distinct clickable links, the entire image is a single link. The destination of that link is a page inserted into hijacked web server (otherwise unused at the moment). That page then redirects any visitor to the phishing page asking for the PayPal user ID and password. Unlike most phishers recently, this guy bought a domain name (99% chance it was with a stolen credit card) and used a free hosting service to put up his phony site. The domain name is one of those lookalikes, where he uses "paypai" to look like "paypal." That is sooo 2004.
For the record, my PayPal account was blocked about a year and a half ago because someone tried (without a "y") to access my account, trolling unsuccessfully for the right password—details here. PayPal does not send out a notice when this happens. You discover it when you try to log into your account the regular way, and you are denied access. PayPal does record the IP address for each account access, but knowing that a South Korean computer tried to hack my account wasn't much help in tracking down the perp. Using a non-public and unique-for-my-PayPal-account email address has solved that problem.
I'm glad to report that in the time I've been writing this dispatch, the hosting service for the actual phishing login page has taken the site down. Woohoo! I'm sure the phisher will soon use another stolen credit card to create yet another domain (if a few aren't already standing by in inventory), and the redirector page will be changed accordingly.
I doubt, however, that he'll buy any English language lessons.
UPDATE (12Aug2007 AM) — Exactly as I had predicted, the same phisher has set up a new site, using a one-character-different domain, still containing "paypai" in the domain name. I haven't received a phishing message yet, so I hope the hosting company (same one used for the first site) is awake this Sunday morning to shut it down before the email drops.
UPDATE (12Aug2007 PM) — With the second site shut down, we're now onto the third "paypai" domain name and site. I wonder how long this game will go on.
UPDATE (13Aug2007 AM) — The third domain/site was shut down last night, and no new one has appeared in its place in the last 12 hours. Oh, poor little phisher.
Posted on August 11, 2007 at 05:33 PMAugust 10, 2007
Huge Spam Spike on 9 August 2007
I was surprised to see that the spam statistics chart showed an outsized jump in spam for the 9th of August—more than twice the usual flow. I had heard rumblings of similar increases from other sources, mostly attributed to stock "pump and dump" spam.
In checking my log for the day, I discovered that most of the jump here was due to backscatter messages—notices that messages sent with my address in the From: field were not delivered to their recipients. In other words, my email address had appeared in the From: field of about 1000 spam messages that could not be delivered to their addressees. Lucky me! This type of backscatter is so bad, that my spam filters unceremoniously dump it to the trash right on the server. In the meantime, the myriad of servers around the world sending these bounce messages to forged addresses waste everyone's bandwidth and server resources.
Come on, email server admins: If the message is spam, quarantine or delete it quietly; if the To: address is not valid, refuse to receive the message immediately, rather than take it in and send a backscatter bounce message. You'll save everyone (including yourselves) a ton of resources.
Posted on August 10, 2007 at 12:35 AMAugust 09, 2007
eBay Phisher Amping Up the Threat Level
One of the eBay phisher tactics is to send a message that tries to look like an official eBay message triggered by a participant in one of your eBay auctions. Legitimate eBay participants jealously guard their feedback ratings. The last thing they want to have happen is an unhappy buyer/seller leaving negative feedback.
In a new eBay phishing message I saw tonight, the phisher throws another log on the threat fire. The message is in the form of the official-looking "Question about Item" mailing that normally comes from eBay's messaging system. Of course, there are a couple of things wrong with the message to the trained eye:
- The entire message is in the form of an image downloaded from a hijacked web site.
- The message fails to address me by my eBay ID, saying, instead, "eBay sent this message to seller."
- The item number in the Subject: line doesn't even come close to matching the item number described in the "body" of the message.
- The link goes to a hijacked web site in the Balkans, not to eBay.
If you're not enough on the ball to recognize these failings, you may be terrified by the message body, which I transcribe here exactly as shown in the image:
Look, There are now 3 months since I paied for the item and I still didn't receive it. This is my last warning : unless you solve the problem the first thing I shall report you to ebay and second I shall go to the police .I am loosing my patience... i will wait your reply !!!
That threat will certainly get some recipients to click on the link to view the item description. The link, as I said, is to a Serbian server, which redirects to not one, but two other servers, eventually landing you at a hijacked Romanian web site, showing the eBay login screen asking for username and password.
Interestingly, if you try to click the link in the message a second time, software planted by the phisher on the Serbian server will not redirect the link to the phony site, but, rather, to the real eBay site (the front page, not the login screen). This tactic, trying to trick (I suppose) antiphishing pholks, is not new (a few malware loading redirectors have been doing this for at least a year), but rather rare among phishing sites. It may be a new feature available in the phishing kits sold by master crooks.
Just another day in the life a social engineer.
Posted on August 09, 2007 at 11:48 PM