| Home | The Book | Training | Events | Tools | Stats |
September 30, 2014
Rewards/Surveys Scams
A lot of retail companies have so-called rewards programs that give customers cash back or discounts throughout the year in return for registering as a shopper with the establishment (usually a chain). You, as a customer, essentially give up highly detailed shopping pattern information each time you go through the register line and show your numbered rewards card.
Many of these companies also encourage customers to sign up for email notifications of special pricing or discounts. It's not uncommon to receive at least one such email each week. After a time, you don't think twice about the validity of the email, especially if it displays many of the same iconography (logos, trademarks, and HTML design elements) from week to week.
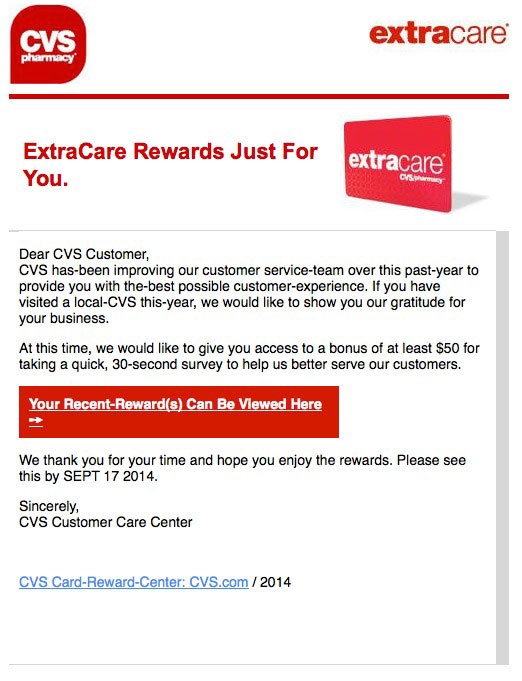
For example, here is an email originating from the CVS Pharmacy chain directed at its ExtraCare rewards program members:
After you have seen dozens of these kinds of emails, the following one comes into your inbox, indicating the sender is "CVS Card Savings" and the Subject: is "Attn:CVS-Card Perks Currently-Expiring! #1421138629":
Because the overall appearance of the second one has plenty of recognizable visual cues borrowed from email messages you've seen before, your instinct is more than likely to consider the second one to be as legitimate as the first.
Wrong!
Ignoring the fact that the message content arrives with an action deadline from a couple of weeks ago, all it takes is a mouse rollover of the active links to discover that the destinations of second message's links are not to cvs.com (like the first message) but to something entirely different. While it is true that some legitimate companies hire outside firms to handle genuine surveys, I can't imagine CVS hiring a firm whose domain name was created one hour before the email message was sent.
I don't know what happens if you start following the click trail from the second email (life is too crowded today), but the consequences for you could range from putting survey money into the hands of the spammer (and don't expect to ever see your bonus reward in return for your wasted time) all the way to more nefarious drive-by downloads/installations of malware on your computers (especially of the unpatched or unprotected Windows varieties).
As a rule, I avoid all survey requests received online (or via telephone robocalls) as if they are capable of sneezing ebola into my face. The more you are promised in return for your participation, the faster you should run away.
Posted on September 30, 2014 at 11:30 AMSeptember 08, 2014
Crooks Trying to Work Around Apple Two-Factor ID
For every attempt by the Good Guys to thwart phishing or security breaches, the Bad Guys will do their best to trick unsuspecting users—and even those who think they know better—into giving up their credentials.
For instance, Apple has recently implemented a two-factor login option that links login attempts to specific hardware registered by users. If you login via one of your registered devices, things run as before. But login attempts from unregistered devices trigger a text message containing a security code that lets you login once from a different device.
If you don't fully understand how all this works, then the following phishing email that arrived this morning might fool you into thinking someone has used your Apple ID to download a $30 Miley Cyrus album (yikes!) from iTunes:
From: Apple
Subject: About your last Transaction
Dear Customer,
Your Apple Email ID, was just used to purchase "´´Bangers´´ Album by Miley Cyrus ($ 29,99 ) from the iTunes Store on a computer or Apple Iphone that had not previously been associated with that Apple ID.
If you made this purchase, you can disregard this email. It was only sent to alert you in case you did not make the purchase yourself.
If you did not make this purchase, we recommend that you go to http://apple.com/support/cancel_pending_transaction to cancel the transaction, Confirm that you're the owner of the account and then follow the instructions.
Apple!,
iTunes
Despite a couple misspellings, the crooks did try to mimic an Apple look via stylesheets: a grey box background for the message body.
Trouble is, the operational link behind the visible one—viewable by rolling the mouse pointer atop the link or, for iOS mail, pressing and holding the link—is to a site that has nothing to do with Apple. Rather, the site is in Indonesia, and has been hijacked by crooks from someplace else. If you were to follow the real link, your browser would be redirected to a URL whose start might fool users into thinking it's Apple, but is, in fact a Brazilian site:
http://apple.com.itunes-login-information-proceed-now-step-one-go1.[removed].com.br/Apple
This just goes to show you that even if you do the right thing, such as sign up for two-factor logins, you must still be hypervigilant against the mind games that crooks use to trick you out of your login credentials. Any time an email arrives from anywhere that talks about logging in or passwords, alarm bells should go off in your head. The only thing you should click for that email is the Delete button. Use your bookmark to access the subject site to see if your account needs attention.