« Netflix Phishing | Main | Another Day, Another Apple ID Phish »
| Home | The Book | Training | Events | Tools | Stats |
June 25, 2018
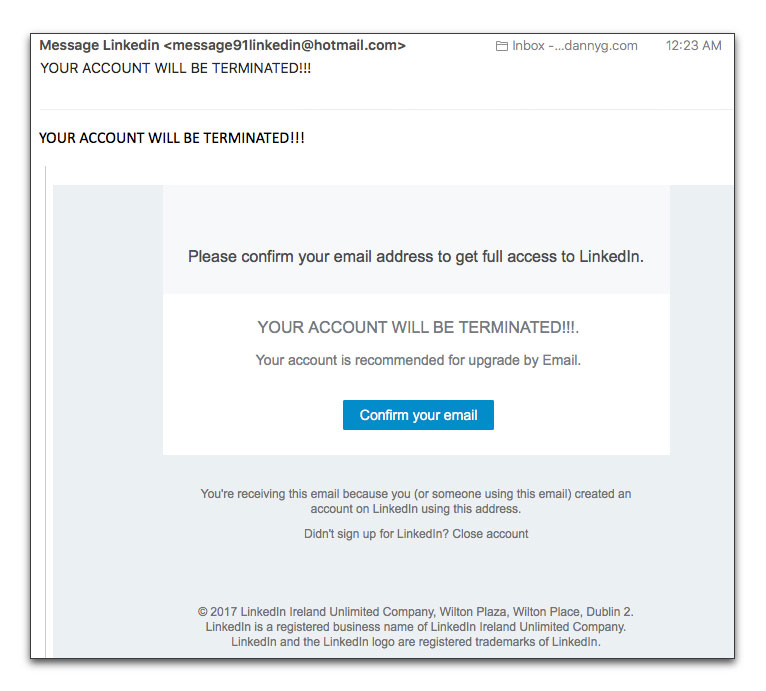
LinkedIn PhishingI am a LinkedIn member at the free account level, but I don't use it much. Thus, when I saw the following message in my Inbox, for a half-instant I wondered if LinkedIn was planning to bounce me for inactivity:
Message LinkedIn YOUR ACCOUNT WILL BE TERMINATED!!!
In the next half-instant, I immediately figured the message was some kind of trick. Unless you start doing something illegal or rant with the "n" word, it's awfully hard to get an account terminated at social media sites. Even after you die or are abducted by aliens.
Here is the message in full:
Although the text is decent English with good spelling, there are plenty of other signals that this message is bogus. Can you spot them all?
- The From: address is a hotmail.com account, not linkedin.com
- The text promises "full access" to LinkedIn as well as something about an upgrade via email. LinkedIn has multiple tiers, but anything other than the basic service is a paid, premium service. They don't give that stuff away.
- You wouldn't know it about this particular message, but it was addressed to me at an email account I don't use for my LinkedIn account.
- The message is copyrighted 2017, rather than the current year.
- This message claims to come from LinkedIn Ireland. Now, the main company is based in Sunnyvale, CA and is owned by Microsoft. They may have an Irish branch, but why would that branch be concerned by my account?
- Rolling the cursor atop the "Confirm your email" button reveals a link to a subdomain at a free web hosting service.
- There is no LinkedIn logo art anywhere in the message. Highly unusual for any business communication from an online business.
For such a short message, this phishing email stinks quite heavily. If you're sloppy in reusing passwords, think about how giving up your corporate email address and password can be. A crook could literally log into your company's system under your userID (probably the same as your email address before the @ sign), at which point a knowledgeable cracker could burrow deep inside the system to steal secrets or disrupt operations.
That, my friends, is why we must all stay on our toes with respect to incoming messages of any kind on any service.
Posted on June 25, 2018 at 09:48 AM