| Home | The Book | Training | Events | Tools | Stats |
November 27, 2004
The Phisher Doth Protest Too MuchI don't know why I've been pounding on phishing scams lately—perhaps it's because they've been pounding on my inbox.
But today's deliveries included a bogus PayPal notice that is really counting on recipients using Internet Explorer for Windows, all unpatched. The HTML message includes a sidebar with this little tidbit:
A genuine PayPal link will always begins with "http://www.paypal.com"
Remember to check your browser's Address/URL Bar to be sure you are on an authentic PayPal site.
Please make sure the link you click on starts with "https://www.paypal.com"
(Note the conflict between "http:" in the first item and "https:" in the last.)
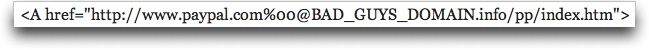
The message displays what looks like a link with PayPal's actual address (with the secure https: protocol), but, as I revealed in the previous entry here, the source code applies the "hex zero" trick that hides the bad part of the address in the IE Address field:
Other wording in the message blares: "This is NOT a SCAM or HOAX. Please check your address bar to make sure you are on the authentic PayPal website." Except that the phisher's site is not served by a secure server, and will reveal "http:", not "https:" in the Address bar, as the real PayPal site does. Of course not many Web users would notice the subtle, but incredibly important difference. I've yet to see a phisher's Web site operate as a secure server, but anything is possible.
Like I say frequently in Spam Wars, the more a spammer or scammer professes honesty, the more likely the opposite is the case.
Posted on November 27, 2004 at 07:33 PM
