« Is spamwars.com Being "Joe-Jobbed?" | Main | Clueless in Bethesda »
| Home | The Book | Training | Events | Tools | Stats |
September 02, 2006
Are Phishing Sites Being Re-Hacked?In the course of my get-the-phishing-site-shut-down activities, I check back with the URLs I report to see how quickly (or if) the sites have been shut down yet. The majority of phishing pages I see come from a legitimate server that has been cracked by crooks who put their bogus stuff in (sometimes partially hidden) subdirectories. Once such a page has been shut down, the site's true owner or ISP sometimes redirects the URL to the site's real home page. Or, more typically, the URL is just left to dangle, returning a standard 404 "Not Found" response to the visiting browser. As long as the crook can no longer gather usernames and passwords from ill-informed victims, anything is okay with me.
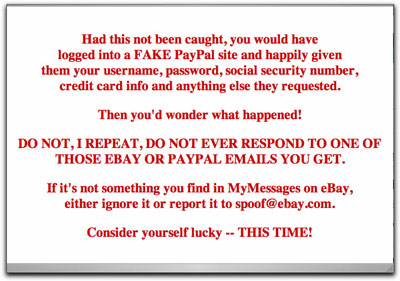
In the last few days, however, I've seen two separate instances in which the original destination page had been replaced by a stern warning to the visitor that by following the link in the phishing message, he/she could have gotten into big identity or credit card theft. Here is one of them:
Now, I'm all for consumer education, but the source of these messages is almost as curious as the phishing attempts. Neither one identifies the source of the message as being associated with the ISP or site owner. You'd think that the site or ISP would want to take credit for having shut down the phony page and alerting potential victims about the scam (although admitting to having been cracked takes some guts).
More curiously, the first one I saw had a completely different look to it, far from perfect English syntax/spelling, and even handed out grades to the phishing crook for his level of proficiency (reportedly quite low) needed to hack the site. This one was "signed," but by someone using the name of a character from the original Star Trek series.
These two separate incidents make me wonder if some anti-phishing folks are fighting back with the phisher's tactics of taking over sites that had been taken over, replacing the bad stuff with, well, less bad stuff.
I won't condone cracking anyone else's site, even if the owner or ISP left the keys in the ignition (read: didn't change default passwords or haven't patched their systems). This is definitely a possible trend to watch.
Posted on September 02, 2006 at 01:02 PM