« New Items | Main | Persistent and Escalating Malware Delivery Campaign »
| Home | The Book | Training | Events | Tools | Stats |
March 15, 2016
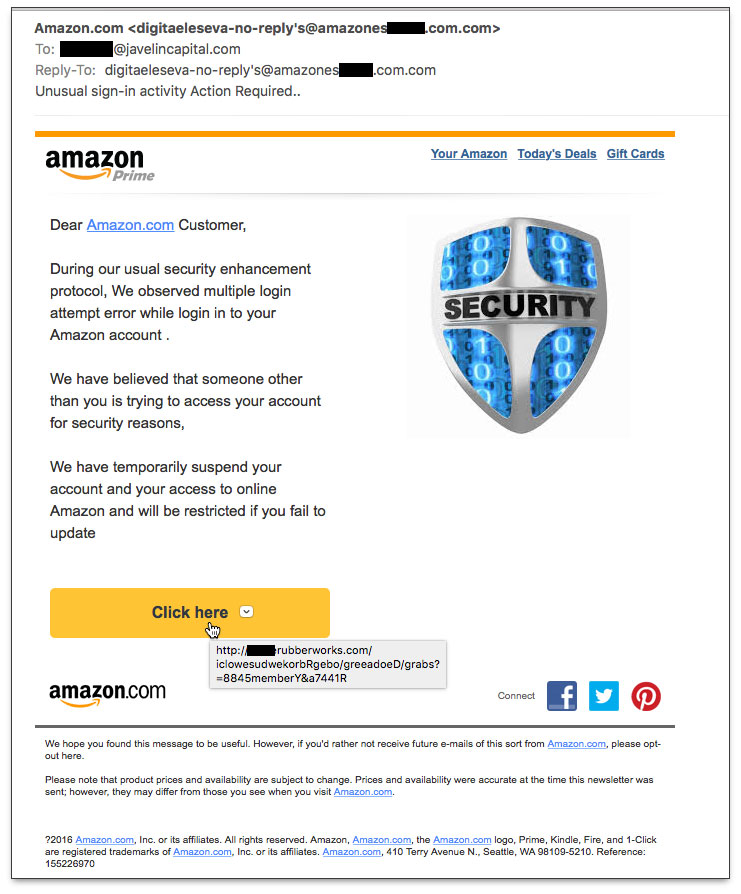
Amazon Unusual Sign-In ActivityFrequent readers of this blog know that I like to expose tricks used by spammers and scammers to get unsuspecting email recipients to hand over login credentials or install malware. Very often the telltale sign of a bogus email is poorly constructed English in the body of the message. And yet it occurs to me that not everyone receiving these emails necessarily has English as a first language. Instead, a fancy email HTML layout and carefully placed key words may be more than enough to trick recipients into clicking on the potentially disastrous action maker in the message.
Here is a case on point:
Years ago, a very talented artist friend of mine told me about the "squint test", which instructs you to look at a graphic through squinted eyes. Your view through this limited aperture provides a quick overall sense of the image's balance, color, and primary focus. It forces you to grab a first impression of the image without seeing too much detail.
Applying the squint test to the above email, the impression is that of an Amazon.com mailing, pure and simple. And then there is that big Security badge image aimed at amping up the alarm of the message. An unsuspecting recipient might easily overlook the bad writing and focus on the alerts about "someone other than you is trying to access your account" and "temporarily suspend your account." Potentially frightening things if you're an active Amazon shopper.
Fear and/or curiosity about the mysterious logins and account suspension are enough to draw plenty of recipients to that "Click here" button.
Now, this message may pass the squint test, but it certainly fails the stink test. It reeks of problems that should be easily detected even by recipients with only modest technical know-how.
First, it is vital that all email users be extraordinarily suspicious of any message (including email, text, or social media message) that claims to signal a problem with any kind of password-protected account. This is especially true for sites connected to your financial information (banking, investments, PayPal, government benefits agencies, insurance, mortgage, credit card companies, etc.) and shopping sites (too many millions to list). Next, I recommend ignoring (i.e., deleting without action) messages claiming to come from brand-name retail and food chains, particularly those with which you don't have ongoing relationships. That Chipotle coupon you think you'll earn by filling out a survey will likely become more aggravating and painful than a bout of E. coli.
But back to our bogus Amazon mailing.
If you're queasy about the threat of a suspended account, the best action you can take is to log into your account by way of a previously saved bookmark to the site. Do not, under any circumstances, click a link in the message to go to the site. Also don't rely on typing the URL to the site into your browser, because you may make a slip that takes you to a phony lookalike site whose domain was explicitly registered to trap sloppy typists. If there is truly a problem with your account, you will be alerted to that fact when you attempt to log in to the legitimate account via the normal process.
Now, allow me to itemize the signals that this email message is sending to invalidate it as being real. I'll start with the most obvious items that don't require any technical expertise or even good English skills (since the message is targeted at English-reading recipients). The only assumption I'll make is that large companies, such as Amazon, Google, Apple, Microsoft, and the like, push their form letter correspondence through layers and layers of writers, editors, customer support staff, and lawyers. It is exceptionally rare for this type of communication from a major corporation to be poorly written, formatted, or coded. It can happen, but the goof would be limited. Moreover, avoiding in-message links still has you covered.
- The message isn't even addressed to me. The To: field has some else's email address at a domain different from mine. That, on its own, is sufficient reason to summarily delete the message.
- By rolling the cursor (or, in a touch-screen interface, tapping and holding) atop the "Click here" button, you can see the destination URL of the big action button. In the screen capture above, I've exposed what you'd see from this particular message. The URL does not take the user to amazon.com. There's no way that some rubber company is Amazon's account update firm.
- For a message that claims to be alerting an individual to a problem with his or her account, the "Dear Amazon.com Customer" salutation is very impersonal. When companies, such as Amazon, need to alert users about their accounts (e.g., an expired credit card), the message body will address the recipient by name. Very often, the message will contain additional personal information fragments, such as the final four digits of a credit card) to indicate the sender actually knows stuff about the recipient, and isn't trolling for shoe size.
- The From: and Reply-To: addresses are suspicious. Although it's not uncommon for automated mailings to supply a From: address indicating that you shouldn't use it to reply to the message (e.g., because that address is either intentionally invalid or isn't monitored), to repeat that same "no reply" account name in the Reply-To: field is goofy. The Reply-To: field is intended to supply a valid email message that the recipient can use to respond to the message if so desired (or email servers can use to bounce messages addressed to invalid To: addresses). Additionally, the word signifying the plural of "reply" is "replies", not the singular with an apostrophe-s attached. A sure sign of a non-English author. The same goes for the all-too-common misuse of collective plural nouns that mysteriously gain "s" plurals (e.g., "informations").
- A further issue with the From: and Reply-To: addresses is the domain. True, the full domain contains the string "amazon", but the true domain is just com-dot-com. The "amazones****" part is a sub-domain wired at com-dot-com to go to a customer's server area. I've hidden part of the subdomain because it is a particularly nasty place, and I don't want anyone reading this to get caught in its greedy, potentially terrifying, clutches.
- We're getting into good knowledge of the English language, now. It starts with the Subject: line. It's missing a period after "activity" and has an extra one at the end. A real mess that would never survive a large corporate vetting.
- Language issues abound in the message body:
- Sentences that end in commas
- Sentences that end in nothing
- Subject/verb disagreement
- Verb tenses from left field
- A seemingly small item is at the very end of the message, where the copyright symbol is represented by a question mark. You can be damned sure that the lawyers would never, ever, ever, let that mistake slide.
Additional nerdy issues also litter this message. For instance, the alt attribute of the img tag used to insert the Security badge image was obviously copied/pasted from another Amazon communication. That's my guess based on the "Kindle Daily Deals" description applied to the image. Oops.
Thus ends the autopsy of the email message that is dead to me—and hopefully to you. The only "Action Required" for this message is to delete it, unclicked.
Posted on March 15, 2016 at 05:50 PM